
If you’re a tier 2 or 3 defense manufacturer or specialty subcontractor that touches CUI, CMMC 2.0 is no longer a future problem. Phase 1 of the rollout is live, self-assessments and SPRS submissions are now real contract conditions, and primes are already tightening requirements on their supply chains. The question is no longer “Do we need to do something?” but rather “What do we do first without disrupting production?”
What CMMC Phase 1 Actually Means for You
Phase 1 focuses on CMMC Level 1 and Level 2 self-assessments, affirmations, and assessment information submissions in SPRS. For many SMB manufacturers, that translates to three practical pressures:
- You must be able to prove you understand your required CMMC level.
- You must be able to show how you’re meeting the mapped NIST SP 800‑171 controls (for Level 2).
- You must be ready for primes or the DoW to question your answers and your evidence.
The DoW estimates that more than 220,000 companies in the Defense Industrial Base Sector will be impacted, and multiple reports show a large readiness gap, especially among smaller contractors. That imbalance creates opportunity for the prepared and real risk for those who wait.
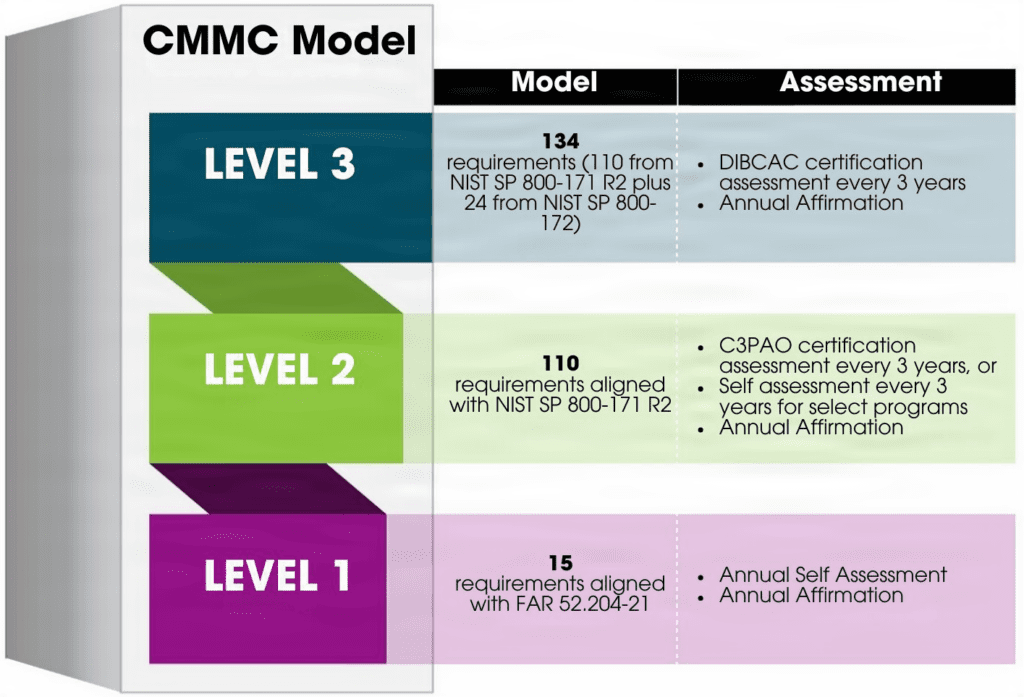
For a concise overview of the formal rule and timeline, you can review the DoW’s CMMC 2.0 resources on the official site. The DOW has outlined the CMMC model this way:
Why Many Manufacturers Are Stuck
Most tier 2 and 3 manufacturers share a similar profile, with less than 250 employees and $5-7M in revenue. Common constraints include:
- Turning 110 NIST 800‑171 requirements into practical, working controls.
- Figuring out “how much is enough” to pass a prime’s review or future assessment.
- Collecting and maintaining evidence without overwhelming already-stretched teams.
The result is troubling: Policy binders that don’t match reality, plans that are never implemented, and leadership that relies on best guesses when they sign off on contracts.
A 30-Day CMMC Phase 1 Action Plan
To avoid such a predicament, Precise Cyber Solutions uses a pragmatic approach with defense manufacturers.
Week 1: Clarify Scope and Level
- Confirm whether you’re targeting CMMC Level 1 or Level 2 based on contract language and CUI exposure.
- Identify where CUI actually lives: engineering repositories, file servers, M365, ERP and MRP, shared drives, and vendor portals.
- Document a simple, written definition of your CUI boundary.
Week 2: Rapid Gap Snapshot
- Run a fast, structured readiness diagnostic against the NIST 800‑171 requirements applicable to your environment.
- Score controls as “implemented,” “partially implemented,” or “not implemented.”
- Identify top 10–15 gaps that pose the highest risk to contract eligibility: access control, MFA, logging, incident response, backups, vendor access, et al.
This forms the backbone of your System Security Plan (SSP) and Plan of Action and Milestones (POA&M).
Week 3: Evidence-First Remediation
- For each priority gap, define the minimum viable control and the evidence you’ll keep (policy, procedure, log, ticket, configuration screenshot).
- Assign clear ownership by role – not by individual name – for each control (e.g., “Internal IT or MSP – access provisioning,” “Operations – physical access”).
- Stand up a simple evidence repository (e.g., SharePoint library) and start capturing artifacts as changes are made.
Week 4: Self-Assessment and SPRS Readiness
- Perform your formal self-assessment based on your updated control status.
- Finalize SSP and POA&M with realistic timelines and responsibilities.
- Validate that leadership understands what they’re affirming and where risks remain.
At this point, you should be able to complete the required SPRS submission with a defensible score that aligns to your documentation and real-world controls.
Avoiding the Biggest CMMC Audit Pitfalls
Across defense manufacturers, the same mistakes show up repeatedly:
- Paper-only compliance: Policies that describe controls that are not actually operated
- Ownerless controls: Person or persons accountable for keeping a control active unknown
- Evidence chaos: Logs and proof scattered across email, tickets, and file shares
- Overdependence on tools: Assuming an MSP’s tools “do CMMC” without governance
A better model is evidence-ready CMMC. Define what “good” looks like, implement the minimum viable control, and prove it with artifacts that would stand up to a prime’s scrutiny or a future assessment.
How Precise Cyber Solutions Can Help
Precise Cyber Solutions works with tier 2 and 3 defense manufacturers, to deliver CMMC readiness without disrupting production. Typical engagements include:
- A fixed-scope CMMC readiness diagnostic and gap plan.
- SSP and POA&M creation aligned with how your plant actually runs.
- Ongoing fractional CISO governance to keep controls and evidence current.
If you’re considering upcoming bids and wondering whether your current posture will hold up, now is the right time to turn CMMC from a contract risk into a competitive advantage. Learn more about Precise Cyber Solutions.
